Core Passkey Technology
Passkey technology has three facets that are all related and are often confused with each other:
- Web Authentication (WebAuthN) is the communication specification (or API) used to perform the authentication ceremony. It defines the messages passed between web servers (also known as Relaying Parties), web scripts running in the browser and calls to the browser APIs. The browser APIs expose two functions that are WebAuthN:
-
Authenticate (navigator.credentials.get()) — used to authenticate the user.
-
Create Passkey (navigator.credentials.create()) — used to create a new Passkey credential for a user.
-
FIDO2 is the full set of authentication technologies. It includes WebAuthN and continues deeper into the technology stack to include how the browser or operating system selects and communicates with any available authenticators
-
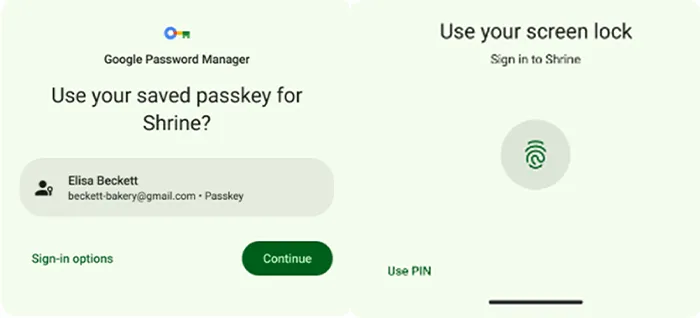
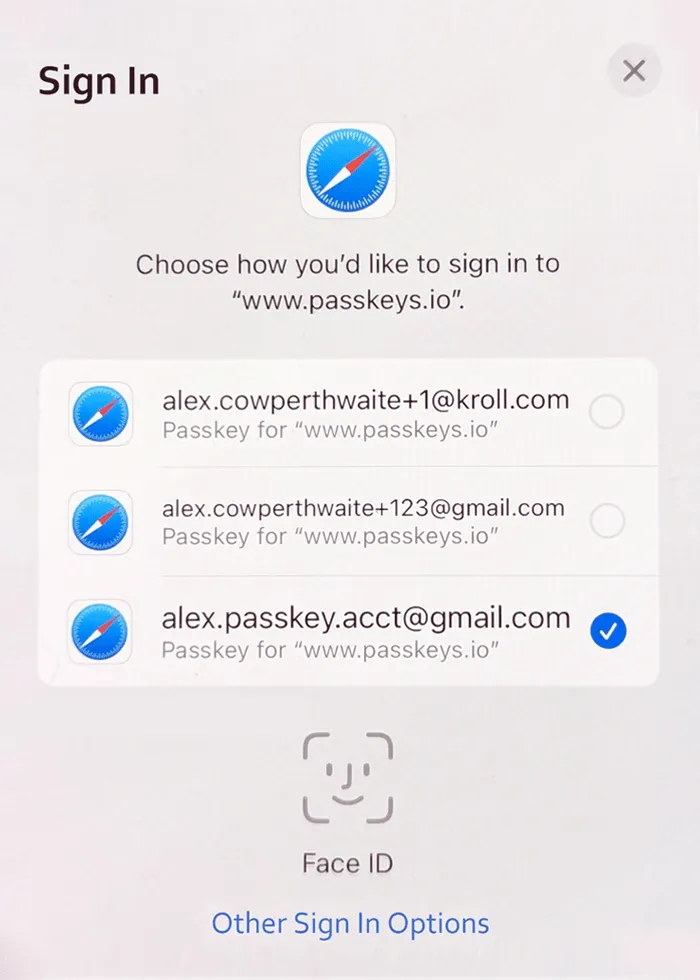
Passkeys are the implementation of FIDO2 by the major platform vendors, agreed upon by the FIDO alliance. The agreement to implement FIDO2 on these platforms allows for strong cross-platform authentication, which is available (or will soon be available) for most users. Passkeys also includes account-based recovery and credential syncing across devices, eliminating significant usability challenges that limited prior technologies.
“Passkeys” is preferred over “FIDO2” when the terms can be interchanged because the adoption by the major vendors is a key to Passkey’s success, and the term is more user-friendly.
Introducing Kroll PasskeyScanner
Passkeys have been adopted by the major platform vendors, incentivizing application developers to build Passkeys into their applications. Vendors such as Adobe, Amazon, Best Buy, GitHub, Google, PayPal, Shopify and TikTok have already deployed Passkey authentication.
Kroll’s Offensive Security team provides penetration testing and other offensive security assessments to clients globally. To ensure that we are equipped to properly assess Passkeys, we have developed proprietary methodology and tooling.
As part of this, we created a BurpSuite extension called PasskeyScanner that helps our security consultants evaluate implementations of Passkeys. This plugin is freely available in the Portswigger Bapp Store to contribute some of our efforts to the community. We also presented a talk at a HackFest event where we released this plugin and gave a more detailed overview of the Passkeys attack surface.