KAPE had a number of key updates during the final quarter of 2021. Here is a recap of all the important enhancements and news from October through December 2021:
Key Q4 2021 KAPE Updates
- Continue update of KAPE and EZ Tools binaries with KAPE-EZToolsAncillaryUpdater.ps1
- KAPE Module reorganization
- Nominate KAPE in the Forensic 4:cast Awards
- Version Changelog 1.1.0.1
- Fix issue with SFTP verification when using --scd and the directory already existed
- Update Targets and Modules
- nuget and control updates
- Version Changelog 1.1.0.0
- Fix Editor and Save As in gkape
- nuget/control updates
- Tweak how KAPE is accessing files in the root of VSCs
- Change sync to accept a GitHub repo (optional) to pull Targets and Modules from. Without specifying a URL, the official repo is used. The URL is expected to have the same format as the official repo should an alternate URL be used.
- Sync will also include .template and .guide files in the Targets and Modules directory
- Fix issue with Disable flush warnings related to mdest existing
- When transferring files, add timestamp to end of directory in format yyyyMMddHHmmss. Example: KAPE_data_push{comment}_yyyyMMddHHmmss, where comment is optionally supplied
- When using Azure SAS, add details to the test file being uploaded (timestamp, computer name, OS info, comment) vs. simply “test upload” for the contents
- Added --scd switch to specify the default path to upload files to. If the directory does not exist, it will be created. Do NOT use leading slash! Example: --scd foo/bar/wizzo
- Update included Targets/Modules and Module binaries
See end of the article for additional updates.
Continue Update of KAPE and EZ Tools Binaries with KAPE-EZToolsAncillaryUpdater.ps1
Kroll’s Andrew Rathbun created a PowerShell script to automate the updating of the KAPE binary and EZ Tools binaries found in .\KAPE\Modules\bin, and he created the ancillary files those tools rely on to generate output. KAPE utilizes Targets (.tkape) and Modules (.mkape), RECmd utilizes Batch (.reb) files, and SQLECmd (.smap) and EvtxECmd (.map) utilize Maps. Each of these files is stored in separate repos on GitHub. Keeping all these components of your KAPE instance updated is now made easier using Andrew’s PowerShell script, KAPE-EZToolsAncillaryUpdater.ps1.
The KAPE Target/Compound Target Guide and Template files were created earlier in 2021. Recently, we added a KAPE Module/Compound Module Guide and Template for the community’s benefit. With guides for both Targets and Modules in place, anyone can follow and create their own Targets and Modules either for internal purposes or to contribute to the public KapeFiles repository.
KAPE Module Reorganization
In late 2020, the Targets were reorganized and standardized, including but not limited to, file-naming conventions, content structure of .tkape files and reorganization of the files and folders within the Targets folder. Modules received this same treatment in November 2021. Modules were renamed to a standardized format similar to how SQLECmd Maps are named. Following is the template and a few examples:
- Template
- .\KAPE\Modules\Apps\ToolName_Description.mkape
- Examples
- .\KAPE\Modules\Apps\NirSoft\BrowsingHistoryView_BrowsingHistory.mkape
- .\KAPE\Modules\Apps\GitHub\Volatility\Volatility_pslist.mkape
- .\KAPE\Modules\EZTools\RECmd\RECmd_Kroll.mkape
The Apps folder in Modules had significant changes during this reorganization. Tools that originated from GitHub were given their own subdirectory (.\Apps\GitHub), and any other tools where there were three or more by either the same developer, suite or process now has a dedicated folder created for them. For example, all NirSoft tools are now in .\Apps\NirSoft. All Sysinternals Modules are stored with one another in .\Apps\Sysinternals. Lastly, there are currently three SOF-ELK Modules (with more to come in due time), so they reside in .\Apps\SOFELK.
Any Modules that relate to processes or tools that ship with Windows were moved to the Windows folder. This includes Modules written using PowerShell since that ships natively with Windows. Additionally, all Modules related to EZ Tools reside in their own dedicated EZTools folder. If there are two or more Modules related to a given tool, they have been combined in their own dedicated folder named after that EZ Tool.
Ultimately, this reorganization and standardization of the file-naming convention allows for KAPE’s Target and Modules to continue to scale while maintaining order and structure as growth continues. If you had local Compound Modules that were calling on other Modules, it may be wise to ensure the filenames in your local Modules (!Local folder) are calling on the correct file names of your intended Modules.
Nominate KAPE in the Forensic 4:cast Awards!
Nominations are now open for the 2022 Forensic 4:cast Awards that cover all of the 2021 calendar year. If KAPE served you well in 2021, please consider nominating KAPE here.
Here is an overview of the changes to KAPE from October 1, 2021 to December 31, 2021.
Targets Added/Updated
- AVG.tkape
- Avast.tkape
- AviraAVLogs.tkape
- Cybereason.tkape
- FSecure.tkape
- McAfee.tkape
- McAfee_ePO.tkape
- SecureAge.tkape
- Sophos.tkape
- Symantec_AV_Logs.tkape
- WindowsDefender.tkape
- BoxDrive_Metadata.tkape
- BoxDrive_UserFiles.tkape
- Chrome.tkape
- CloudStorage_All.tkape
- CloudStorage_Metadata.tkape
- CombinedLogs.tkape
- Discord.tkape
- Dropbox_Metadata.tkape
- EvidenceOfExecution.tkape
- GoogleDriveBackupSync_UserFiles.tkape
- GoogleDrive_Metadata.tkape
- LogMeIn.tkape
- MicrosoftStickyNotes.tkape
- MicrosoftTeams.tkape
- Notepad++.tkape
- OutlookPSTOST.tkape
- pCloudDatabase.tkape
- RemoteAdmin.tkape
- Signal.tkape
- Slack.tkape
- SOFELK.tkape
- SQLiteDatabases.tkape
- SRUM.tkape
- SumatraPDF.tkape
- SupremoRemoteDesktop.tkape
- USBDetective.tkape
- Viber.tkape
- WindowsPowerDiagnostics.tkape
- WindowsSubsystemforAndroid.tkape
Modules Added/Updated
- Most Modules were moved, renamed or updated in some fashion in November 2021. Be sure to keep your copy of KAPE synced and updated.
KAPE-Related GitHub Repositories
Our experts recommend “watching” the GitHub repositories for KAPE-related updates. Be sure to check the “All Activity” option in the Notifications section (Figure 1).
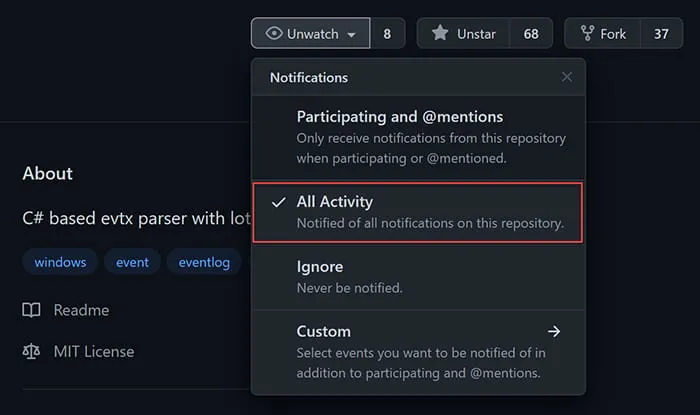
Figure 1 - Notification options
- KAPE Targets and Modules
- Registry Explorer/RECmd Plugins
- RECmd Batch Files
- SQLECmd Maps
- EvtxECmd Maps
- All of Eric Zimmerman’s GitHub repositories
If you need additional KAPE support, explore our virtual live training and certification opportunities or contact our experts at [email protected]. An enterprise license is required when KAPE is used on a third-party network and/or as part of a paid engagement.
This article was written by Andrew Rathbun, a Senior Associate in Kroll's Cyber Risk practice.






